
Dark endpoints: an invisible threat to your IT team
4.7 (309) In stock

4.7 (309) In stock
Invisible devices create significant blind spots that can leave IT departments helpless to act against a breach until it is already too late. A new report from Absolute found 13% of enterprise devices aren't connected to the corporate domain.
The Absolute platform delivers self-healing endpoint security and always-connected IT asset management to protect devices, data, applications and users — on and off the network.
What Is Endpoint Detection And Response? (And Why It's Important)

Julia Sustakova on LinkedIn: Dark endpoints: an invisible threat to your IT team - Absolute Blog

Battling the Invisible: Advanced Malware and Ransomware Defense

Prevent Ransomware Attacks on Your Organization

Protecting Yourself: Privacy, OSINT, and the Dark Web

Cybereason XDR: 10X Faster Threat Hunting

Overlooked Endpoint Devices Are the New Frontiers of Cybersecurity
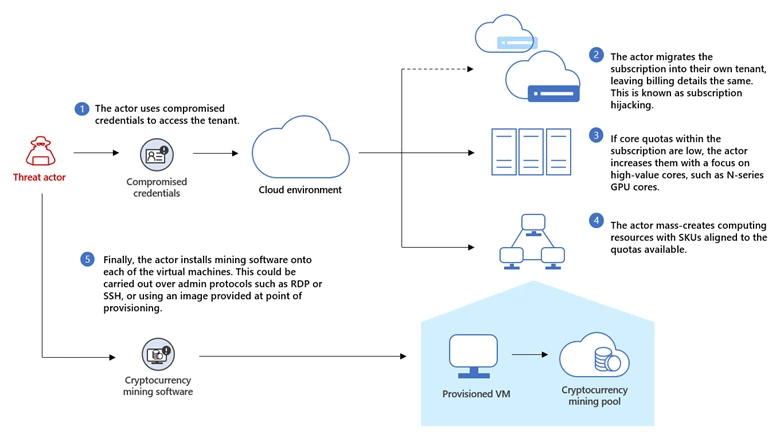
Cryptojacking: Understanding and defending against cloud compute

Unweaving A Complex Web of Threats

Cyber Security - The Driz Group Official Blog - The Driz Group

To protect against ransomware, secure your entire web attack

P3: MS Defender for Endpoint - Threat and Vulnerability Management (TVM)