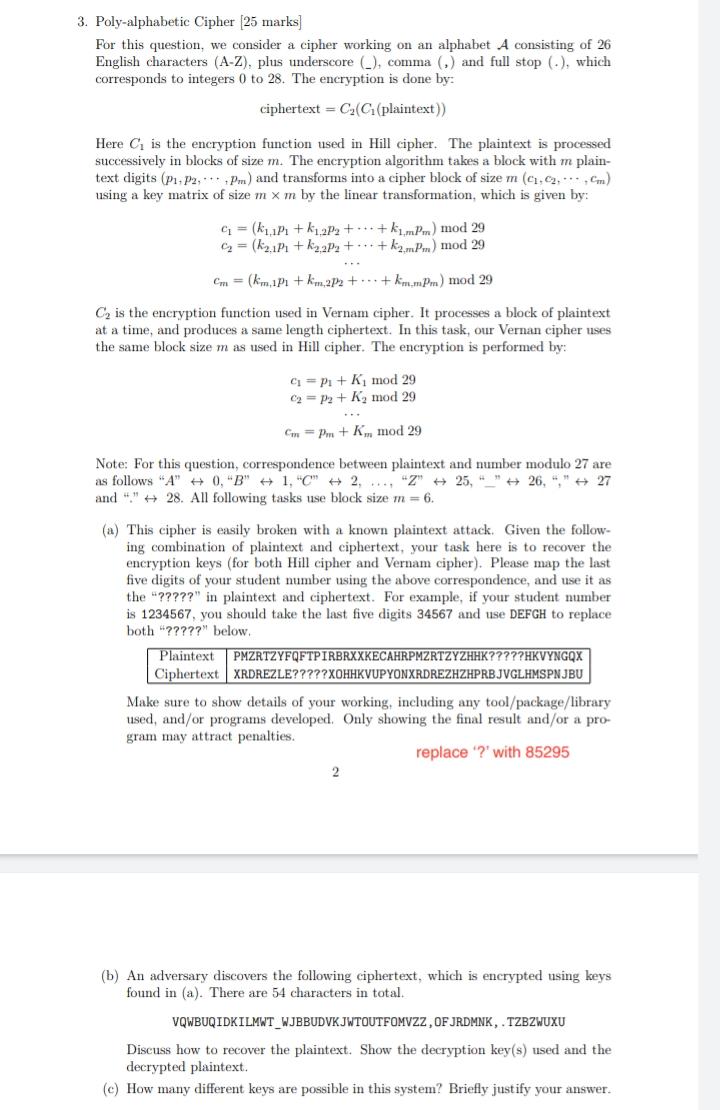
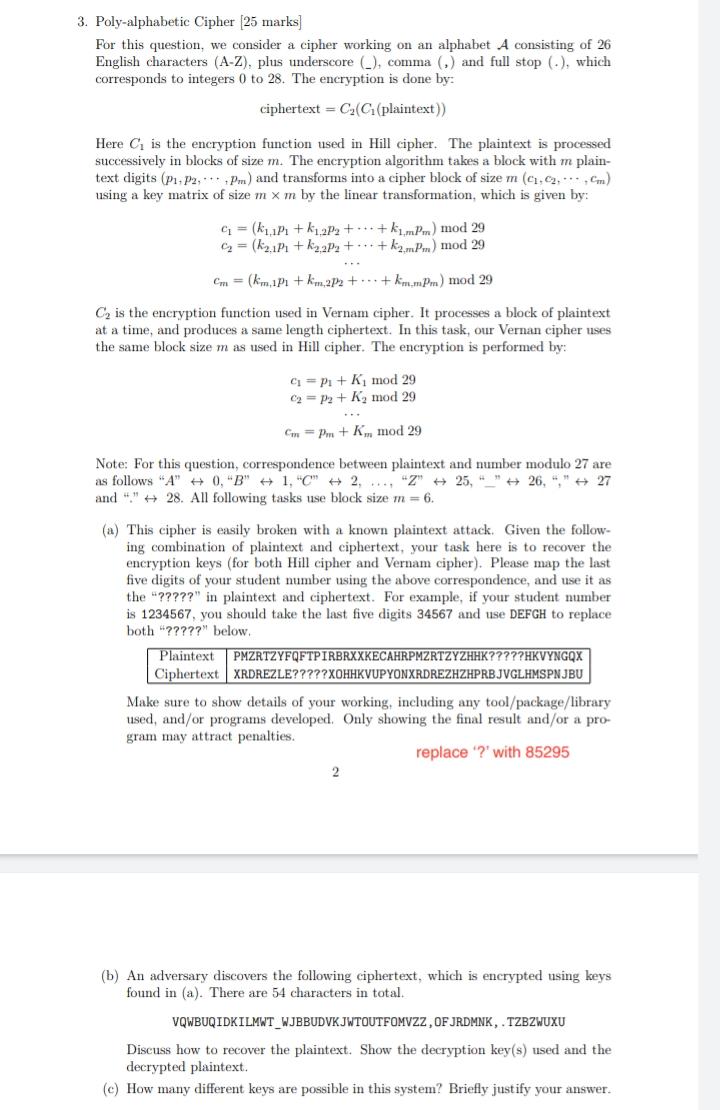
Solved 3. Poly-alphabetic Cipher [25 marks] For this
4.7 (736) In stock
4.7 (736) In stock
d20ohkaloyme4g.cloudfront.net/img/document_thumbna
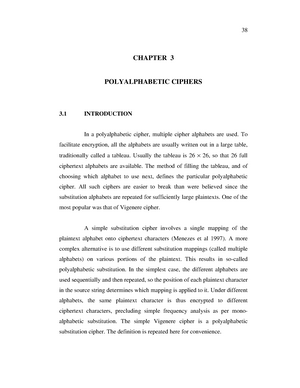
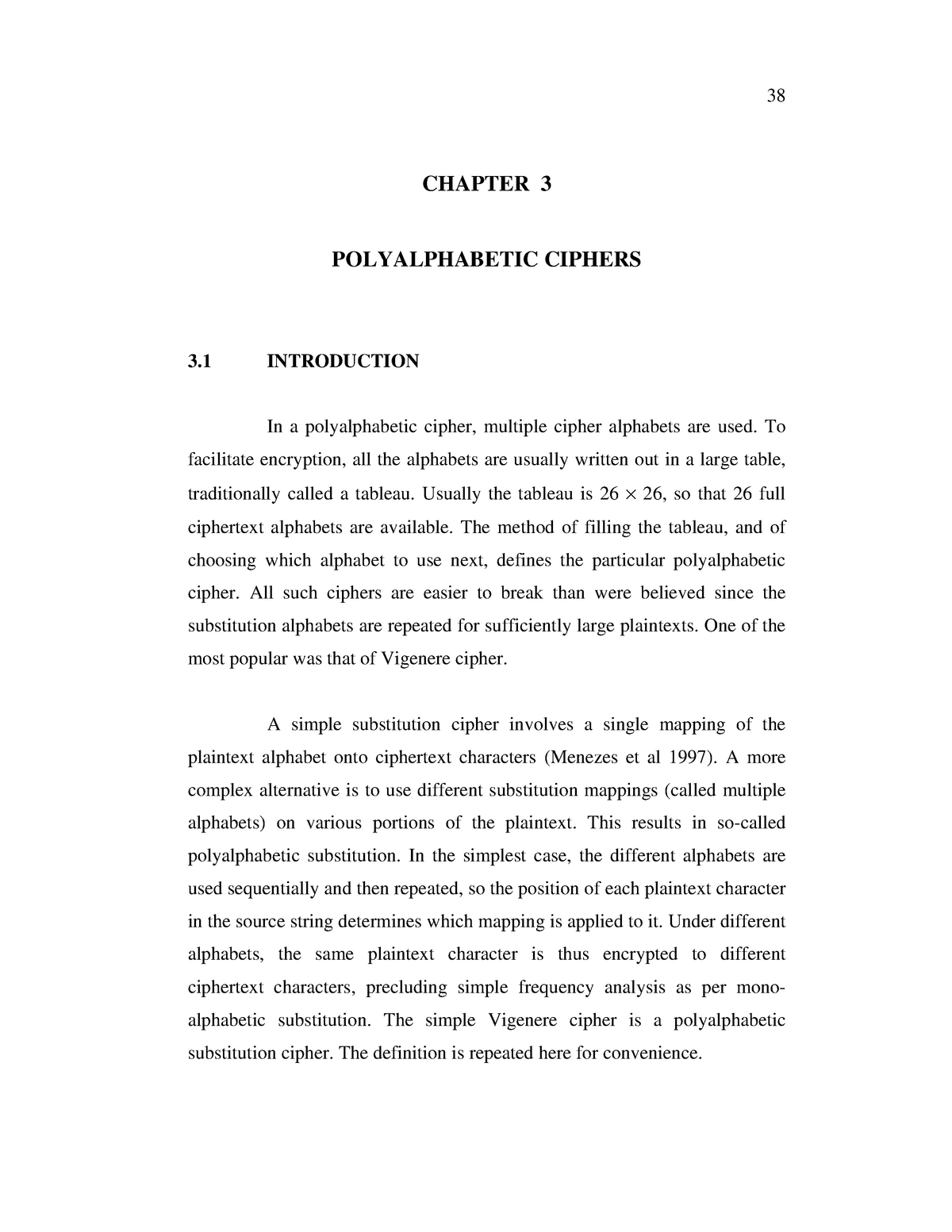
08 chapter 3 - Lecture notes 1 - CHAPTER 3 POLYALPHABETIC CIPHERS 3 INTRODUCTION In a polyalphabetic - Studocu

Cryptography for Dummies — Part 3: Polyalphabetic Ciphers, by Niloo Ravaei, Blockgeeks
PPT - Cryptography : from substitution cipher to RSA PowerPoint Presentation - ID:505822

Polyalphabetic Substitution Cipher

Symmetric Ciphers Questions and Answers, PDF, Cryptography
Cryptology - I: Homework 1 - Mono- and Poly-alphabetic Ciphers
Solved] Encrypt the message using polyalphabetic cipher, given key =
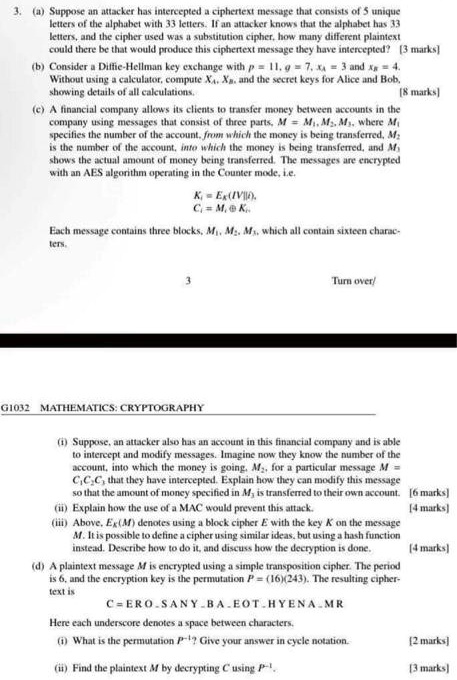
SOLVED: Text: The alphabet consists of 26 letters. If an attacker knows that the alphabet has 26 letters and the cipher used was a substitution cipher, how many different plaintexts could there
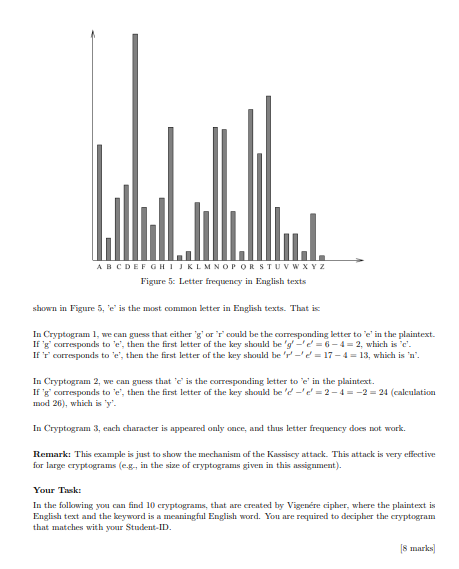
Solved 4. Cryptanalysis of a Polyalphabetic Cipher: In this

Classical Encryption Techniques
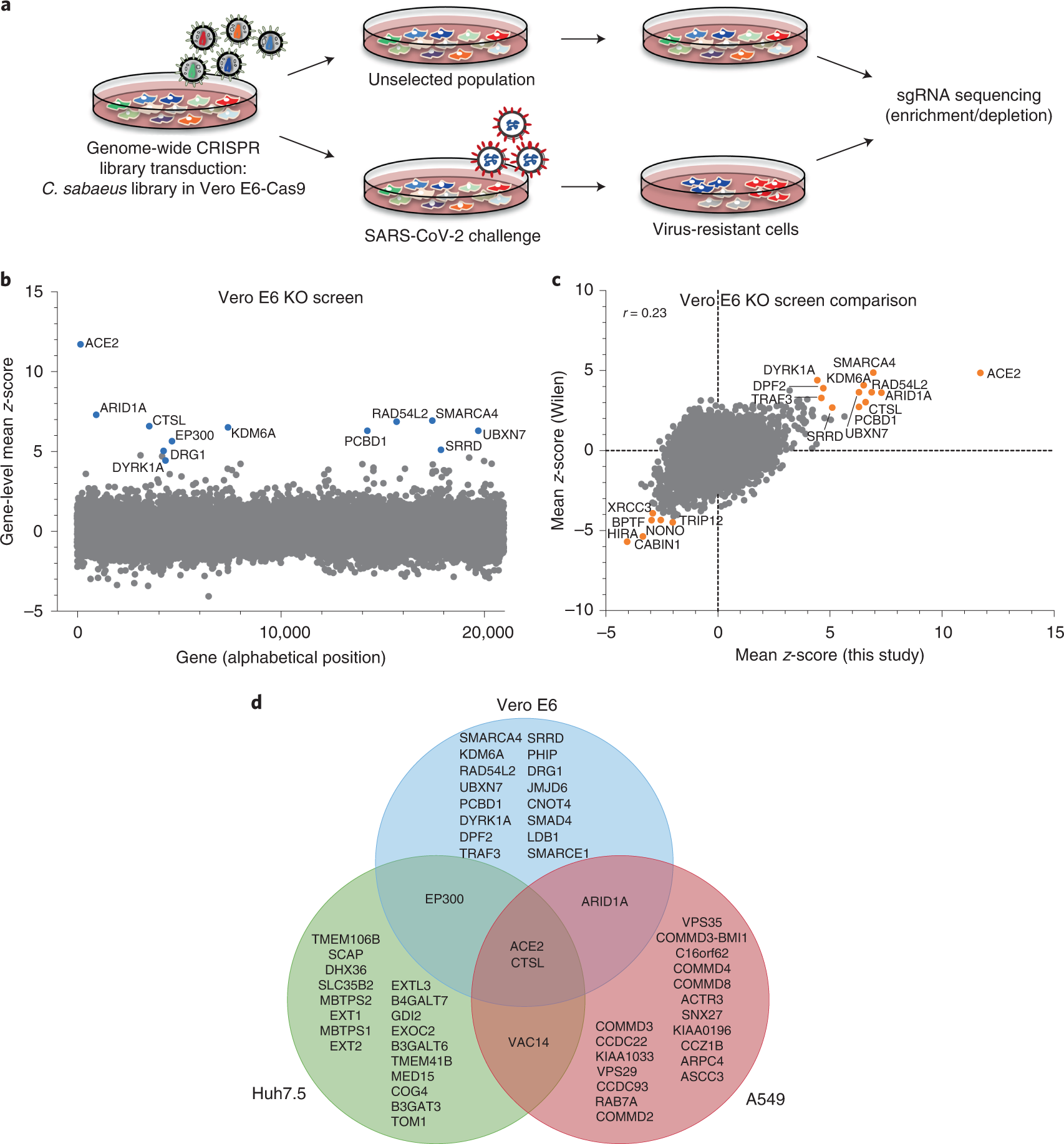
Bidirectional genome-wide CRISPR screens reveal host factors regulating SARS-CoV-2, MERS-CoV and seasonal HCoVs